Cybersecurity, like home security, helps prevent unauthorized access to your most valuable assets, such as your network, computer systems and personal or sensitive information, from cybercriminals and attacks. With the right safety measures in place, you can protect your data from falling into the wrong hands. Learn more about cybersecurity and different types of cyber-attacks so you and your family can browse the web without worry.

Why is Cybersecurity Important?
As our work, school and home lives become more dependent on internet-enabled devices, simply having a strong password isn’t enough to keep devices and data safe. Today’s internet users need sophisticated, continuous cybersecurity for every device and activity. To protect your devices and information, take advantage of any cybersecurity services or add-ons included in your internet plan and only use password-protected networks.
Types of Cyber Attacks
Many types of cybersecurity threats exist in today’s world, such as malware, phishing, ransomware and even state-sponsored cyber attacks. Understanding these varieties makes it easier to protect your network and devices against them. Below are a few of the most common attacks users experience.
Social Engineering
To gain control over your computer system or access personal and financial information, hackers use social engineering, a form of psychological manipulation, influence and deception, in the hope that you’ll make a security mistake and provide sensitive information. Attackers pose as a trusted authority, then use deceptive tactics to steal information (addresses, phone numbers, social security numbers), passwords, banking information and more.
Phishing
The most popular form of social engineering involves sending SMS messages or email from what appears to be a reputable source, such as your bank. The message entices the user to click a link to a malicious site, download an attachment that contains malware or share personal information.
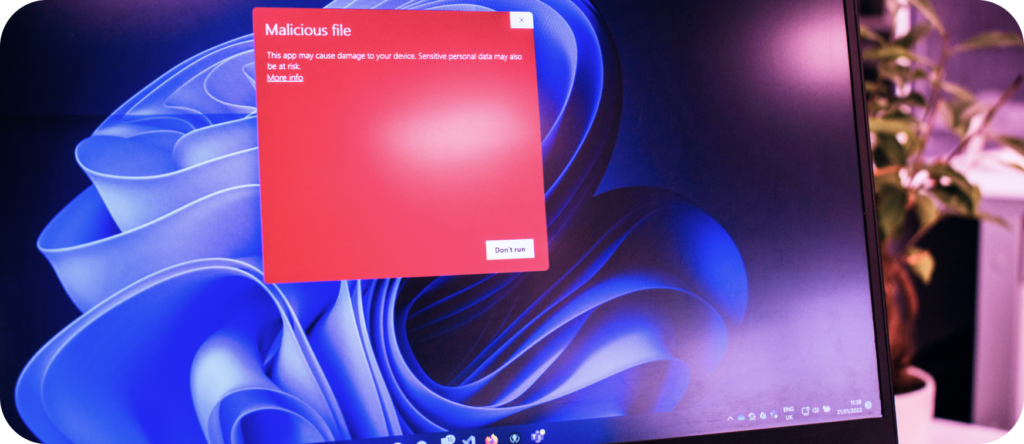
Malware
Malware, short for malicious software, is any software designed to inflict harm on a user’s computer or network, such as stealing passwords or money. Common types of malware are viruses and spyware.
Ransomware
A type of malware that locks or destroys a user’s data unless a ransom is paid to the perpetrator. Cybercriminals encrypt files on your computer and only give you the code to access your information if you make the payment.
How to Protect Your Network from Cyber Attacks
When it comes to cybersecurity, the best defense is a good offense. Along with a network-level security application like Internet Security, powered by ProtectIQ® (included with Wi-Fi plans of 500 Mbps and up), you can protect your network from breaches with careful attention to your hardware and software.
Hardware Protection Tips
- Regularly update your firmware with the latest release of new security patches.
- Encrypt your hard drive to prevent unauthorized users from gaining access to your data.
- Use two-factor authentication to verify the identity and credentials of users, devices or applications that access your network.
- Dispose of your old or unused hardware properly. Some computer manufacturers and electronics retailers take drop-offs or mail-ins, who then dismantle the computers to be recycled.
Software Protection Tips
- Install antivirus software on all devices connected to a network.
- Create a strong password and change it regularly.
- Enable firewalls to prevent unauthorized access and block malicious traffic.
- Avoid phishing and malware that can damage, delete or steal your data.
Common (and Dangerous) Cybersecurity Myths
With threats becoming more sophisticated and common, it’s vital to be aware and educated on cybersecurity to protect yourself and your data. Here are some common misconceptions to avoid:
- Only important people and companies are targets: Hackers use computer programs that automatically search the web for vulnerable devices and networks, meaning they don’t have to target you specifically to gain access to your personal data.
- Strong passwords are enough: Any password can be compromised. Two-factor authentication adds a layer of defense between a threat and your sensitive information.
- You’ll know when your computer is affected: Modern malware is much stealthier than its predecessors. You might not notice an impact on your device’s speed or performance or see strange files or pop-ups.
- Your browser can protect you: While some browsers are more secure than others (such as Firefox and Google Chrome), no browser can protect against all forms of malware.
- You have to open the corrupted files to become infected: Some viruses can get into your system just by being sent to your device, whether you open the suspicious message or not.

Enhance Your Lumos Wi-Fi Plan with Extra Network Security
When you combine the speed and power of fiber internet with the protection of Lumos cybersecurity upgrades like Internet Security, the possibilities for your digital life are limitless.
Check for Lumos Fiber near you and experience the latest in home network security and online connectivity.
Find out if Lumos Fiber Internet is available for your home.


